Securing your store


Lock everything down
As your sales increase, the warehouse gets busier and you are ensuring your own stock flow doesn't run dry - something that can easily be overlooked is security. Whilst you are running around running the business, there could well be someone trying to break in - and if that happens, a profitable peak season can rapidly become a peak disaster.
Protecting your store means two things,
- Protecting customers
- Protecting revenue
Your customers are your priority, ensuring they've got the utmost confidence in your service will guarantee repeat business - and through this, you can maintain sales. So oddly the goal is to both look secure and behind the scenes, be secure.
Contents
- Look secure
- SSL
- Site seals
- Be secure
- Network security
- Firewalling
- Access and encryption
- Store isolation
- Magento core patches
- Keeping up to date with Magento news
- Security check-list
Look secure
When customers view your site, you have a limited opportunity to instil trust; there's a huge level of detail that could be delved into (and probably some significantly more detailed articles), but covering the basics is a simple, quick win.
To the average user, they've been trained to recognise three key signs of a secure website,

The padlock
Buy a standard SSL certificate, have your hosting company install it, and enable HTTPS on your store. Its that simple. A standard SSL certificate costs £15/year.
Weighing up whether to go SSL site wide is a decision that needs careful thought and it isn't a change I'd recommend immediately before peak, the 301 redirection SEO cost could impact you more than the benefits.
The "green bar"
Upgrade your standard SSL certificate to an EV certificate. It can take a few days for these to be issued, so don't wait until expiry of your existing certificate before pursuing it. An EV certificate starts at £130/year.
The security seal
These are often included with all SSL certificates and are also often provided with standalone PCI security scans.
Be secure
The gloss of looking secure may be enough to convince your customers on the surface, but you'll also need to be secure. There'll be nothing worse than promising all the security in the world - and customers being informed by their card provider that it has been fraudulently used as a result of using your store.
Securing a Magento installation
Security starts at an infrastructure level and ends with your store - and any weak link in that chain is going to result in an insecure store. So your first focus needs to be on your hosting provider.
I hate to shamelessly promote our services (or equally, shamelessly undermine other providers) - but there are some basics that should be put in place to ensure your store is secure - some of which are what make the majority of cloud, VPS and even dedicated hosting completely insecure.
- Lock down the infrastructure (if you are using MageStack you are already covered)
- Restrict who has access to your code
- Control access to your admin area
- Monitor file changes
- Maintain a good vetting policy for new developers and staff
- Keeping software patched/up-to-date
There is a thorough article on hardening Magento when using MageStack - and for those using other providers, I've done a deep-dive on achieving similar functionality on Stack Exchange.
All your servers need to be in their own VLAN
If your servers aren't in their own VLAN, it means your network traffic is shared with that of other servers; the impact is that others can potentially sniff your traffic and read plain text traffic (like FTP, or MySQL) - or worse, steal your IP address and perform a MITM (man in the middle) attack.
>All Sonassi solutions have a VLAN as standard. Ask your provider if you have your own VLAN.
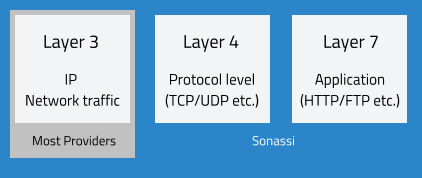
Multi level firewalling is a must
Traditional standalone hardware firewalls are becoming a thing of the past; their usefulness is declining because of their limited capacity, easy nature of being targeted for DOS attack (that's right, firewalls don't protect you from a DOS attack, they often are the first component to fail) and shallow intelligence when inspecting web traffic.
A traditional firewall will monitor very basic traffic, but isn't always capable of detecting or mitigating things like SQL injection, XSS attacks or application level exploits. So if your store is protected by just a basic Cisco ASA (or otherwise), its probably not as well protected as you think it is (or even at all).
>All Sonassi solutions have a 3-Layer firewall as standard. Ask your provider if you have a WAF.
Restricting access and data transfer
When you've got a firewall in place, it immediately becomes useless if you open ports to allow plain-text traffic like MySQL and FTP through it; or expose web services like PHPMyAdmin.
An essential feature of securing your environment is to restrict access by using a VPN; this "first hop" will encrypt your traffic - allowing you to use insecure protocols like FTP. VPN's also have an added benefit of giving granular access control above that of the service being connected to.
>All Sonassi solutions have a VPN as standard. Ask your provider if you can restrict access via VPN.
Separate environments for staging/dev/uat
Your development and staging sites are as much of a target as your live store is; so the less you have exposed to the internet, the better. It isn't a major problem having a single server for live and development purposes (and isn't even a violation of PCI v3 6.4) - provided that you adequately separate the environments.
This means that the code on your live site shouldn't be able to modify/view that on your staging site and vice versa.
>All Sonassi solutions isolate environments via domain-groups as standard. Ask your provider if your sites are 100% isolated.
Be PCI compliant
A single paragraph alone isn't going to do this justice; but I'll summarise the important points. PCI compliance is very often misunderstood because the majority of merchants believe that they are PCI compliant by virtue of using a hosting provider that is; this isn't the case.
It is a merchants responsibility to be compliant - you must contact a QSA (qualified security assessor), complete a SAQ (self assessment questionnaire) where appropriate and undergo regular compliance scans from an ASV (approved scanning vendor). It isn't just a case of saying that you operate a secure practice, but also implement it (by rotating passwords, isolating environments, protecting customer cardholder information etc.)
If you haven't completed a SAQ yet, or don't know what a QSA is - priority number one for you is to engage an approved scanning vendor (like Security Metrics); who can guide you on what the next steps are for a business of your size.
>All Sonassi solutions use MageStack, built to meet PCI v3 regulations as standard. Ask your provider if your solution does.
Patches
Like most applications, Magento has its vulnerabilities - and Magento address these in two ways,
- Security patches
- Magento updates
As most merchants will know, upgrading to a newer version is not a simple task; which is why the alternative of maintaining the security of your store via patches exists.
The patch files that Magento release are in the form of a script that is executed via SSH to fix the core; often they need to be followed up by a series of adjustments in your own customisations (be it modules you have installed, or the theme you use). Applying patches isn't an easy process, but it is essential for security - and is a considerably easier task than cleaning up a store than has been compromised.
Verifying whether your store is patched properly is easily done with MageStack, take advantage of the built in Magento Vulnerability Scanner to identify installations with missing patches. Then downloading and applying patches is made just as easy when using MDA (Magento Download Archive).
Read more about Magento's security program.
Keep up to date
Keeping Magento up to date is one thing, but its no use if you aren't up to date with the latest changes happening with Magento. There are many Magento blogs, news sites and podcasts.
I can wholly recommend subscribing to MageTalk - its a great way to absorb what's happening with Magento from a pair of enthusiastic and experienced Magento developers - or if reading is more your style, check out MageDev Weekly and the official Magento Community Digest.